Hybrid BCS Part 5 – Validation
 Tuesday, September 22, 2015
Tuesday, September 22, 2015- By : Mike Maadarani
 0 comment
0 comment
Now that you have created an external list or deployed an app for SharePoint in SharePoint Online, you need to test the security you put in place. Every account that will be accessing and manipulating the external data must have three properties:
- It must have user or greater permissions to the SharePoint Online site and the external list or app for SharePoint.
- It must be a federated account.
- It must be a member of the on-premises global security group that you are using to control access to the OData service endpoint. For example, it must be a member of ODataGroup.
In this procedure, you will open the SharePoint Online site and the external list or app for SharePoint with four different accounts.
To validate security on the BCS hybrid
- Identify or create one account for each of the account types listed in the following table.
|
Account |
Expected outcome |
Troubleshooting step |
|
Account A
|
External data displayed and editable. |
If the external data does not display or you cannot edit it, check the site permissions, your federation setup, and the membership of your on-premises global security group; for example, the ODataGroup. |
|
Account B
|
External data does not display. |
If the external data does display and you can edit it, check the site/list/app permissions. |
|
Account C
|
External data does not display. |
If the external data does display and you can edit it, check your federation setup and membership of your on-premises global security group (Odata Group). |
|
Account D
|
External data does not display. |
If the external data does display and you can edit it, check the membership of your on-premises global security group (ODataGroup) and the permissions that you set on the OData service endpoint that you configure in Prepare the SharePoint Online environment for the Business Connectivity Services hybrid scenario |
- Open (by using In-Private browsing if possible) the SharePoint Online site that contains the external list or app for SharePoint by using each of the accounts in turn. Be sure to completely log out and close your browser in between tests.
- If you don’t see the expected outcome, refer to the troubleshooting step in the previous table, fix the issue, and repeat all four tests until you achieve the expected outcome.
If you see the error message:
ResourceBudgetExceeded, sending throttled status code. Exception=Microsoft.SharePoint.SPResourceBudgetExceededException: ResourceBudgetExceeded at Microsoft.SharePoint.SPResourceTally.Check(Int32 value) at Microsoft.SharePoint.SPAggregateResourceTally.Check(SPResourceKind kind, Int32 value) at Microsoft.SharePoint.Client.SPClientServiceHost.OnBeginRequest()
You can either remove the throttling:
$webapp = Get-SPWebApplication -Identity http://<URL of your on-premises farm>
$rule = $webapp.AppResourceTrackingSettings.Rules.Get([Microsoft.SharePoint.SPResourceKind]::ClientServiceRequestDuration)$rule.Remove()
Or change the throttling value:
$webapp = Get-SPWebApplication -Identity http://<URL of your on-premises farm>
$webapp. AppResourceTrackingSettings.Rules.Add([Microsoft.SharePoint.SPResourceKind]::ClientServiceRequestDuration, 150000, 150000)$webapp.AppResourceTrackingSettings.WindowCount = 10$webapp.AppResourceTrackingSettings.WindowSize = [System.TimeSpan]::FromSeconds(30)
$webapp.Update()
Note: 150000 is time in ms (ergo, 150 seconds).
Troubleshooting the hybrid configuration
- Verify that the external data source is running and accessible
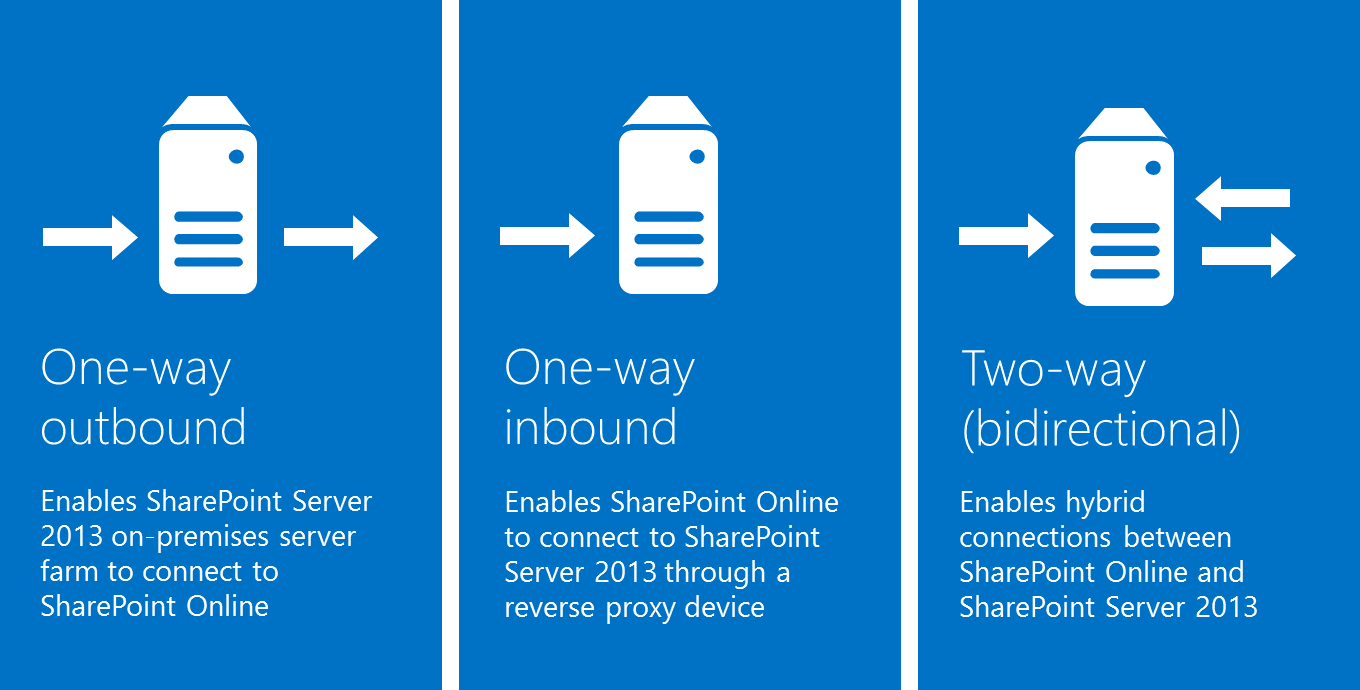
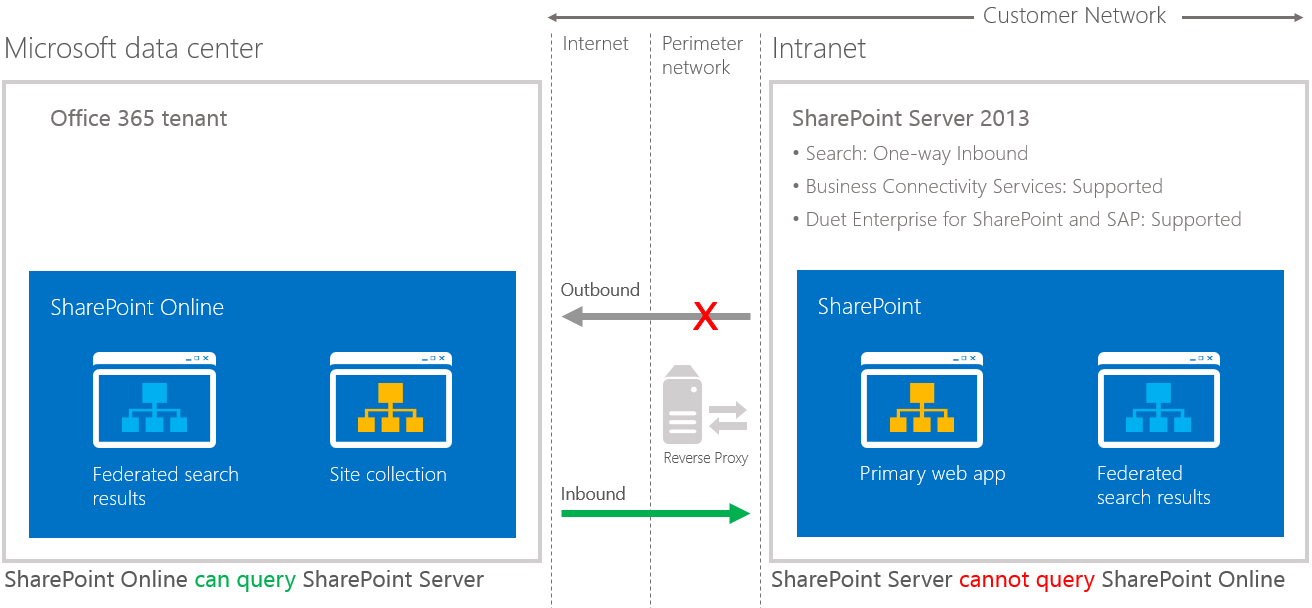
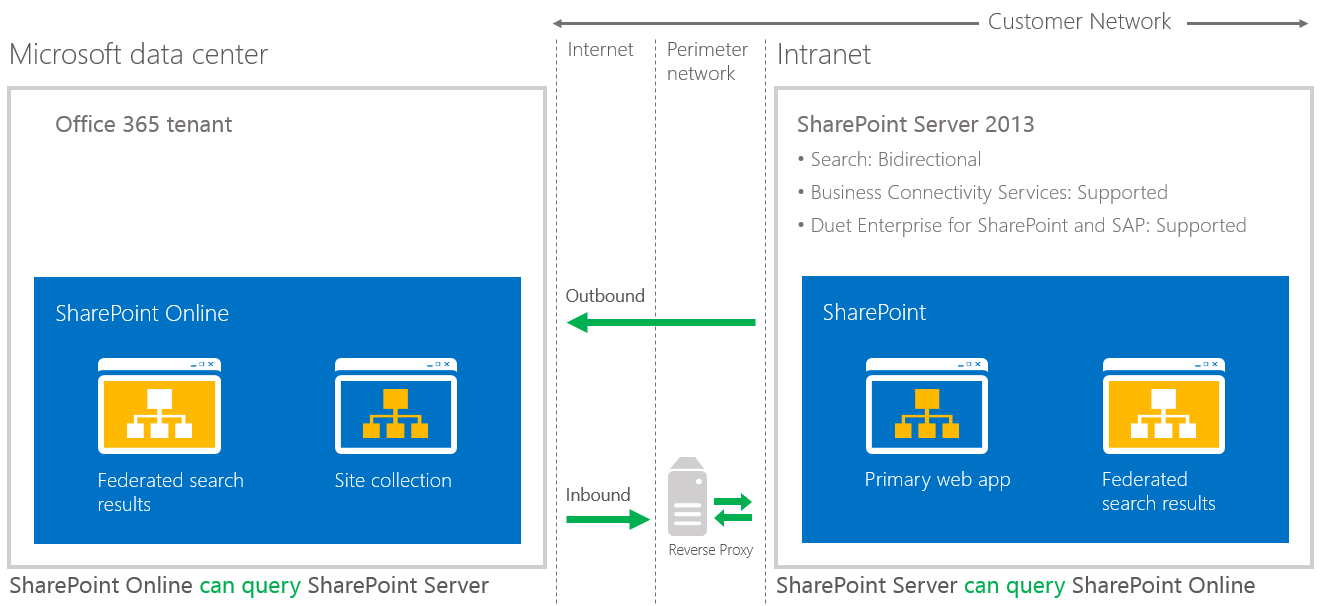
- Verify that one-way outbound or two-way authentication is working
- Verify configuration steps presented earlier
- Check logs written by the Unified Logging Service (ULS logs or trace logs)